Normally, I don’t venture into book reviews, but “Mastering Microsoft Intune” by Christiaan Brinckhoff and Per Larsen compelled me to make an exception. Why? For anyone serious about Windows 365 and Microsoft Intune, this book is a crucial navigator to where you want to be. If you’re an IT pro, it definitely deserves some real […]
Category: Enterprise Mobility + Security
macOS App Deployment with Microsoft Intune: An In-Depth Guide
In today’s modern workplace, where macOS is becoming more popular, the ability to deploy and manage applications is crucial. Microsoft Intune offers powerful and versatile solutions for managing macOS applications, enabling organizations to automate the deployment process, enforce security policies, and provide centralized management. Introduction to macOS App Deployment with Microsoft Intune This guide aims […]

Managing macOS with Intune: Into the belly of PLIST files
Most of my blogging journey has been all about Microsoft Intune and Windows devices – But hey, change is the spice of life, or so they say. So, this year, I decided it’s time to mix things up a bit. I’ve jumped on the macOS bandwagon, got myself a shiny new Apple device, and have […]

Revamping Network Drive Mappings on macOS with Intune
Today, we’re once again diving into deploying network drive mappings on macOS with Microsoft Intune, but with a twist! We’re showcasing an enhanced version of the previous shell script that’s been turbocharged with new features and improvements. Fasten your seatbelts – it’s time for an upgraded ride in the world of automation. You can read […]

Deploy Network Drive Mappings on macOS with Microsoft Intune
Update: Check out the new version of this script. Turbocharged with new features and improvements Revamping Network Drive Mappings on macOS with Intune Welcome, fellow tech adventurers, to the world of macOS management with a dash of Microsoft Intune magic! Today, we’re going to explore how you can deploy network drive mapping on macOS devices […]

Still going passwordless
Last year, I had the opportunity to do in-person presentations about going Passwordless and also wrote many blogs about this topic. In this post I wanted to share some of the information I talk about during these presentations and give you a better idea of why you should consider going passwordless. I will also share […]

Microsoft Ignite 2022
In this post I’ll focus on the highlights and announcements around Microsoft Intune and Security during Microsoft Ignite 2022. I will also try to give an impression of my experiences during Ignite 2022. Microsoft Ignite 2022 (Oct 12 – 14) was perhaps different than any other Ignite I attended before but looking back I’m still […]
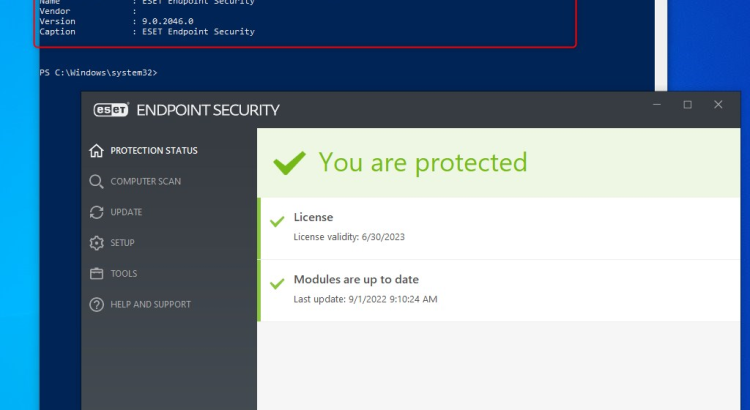
Uninstall ESET Endpoint Security with Intune Proactive Remediations
This is going to be a short blogpost showing you how to uninstall ESET Endpoint Security with Intune Proactive Remediations. I was working on a project where the customer had Windows 10 and Windows 11 devices enrolled with Microsoft Endpoint Manager (Intune) but still used ESET Endpoint Security. One of the requirements was to migrate […]

Working passwordless on Mobile devices
In my previous post “What is your excuse for passwords”, I wrote about going passwordless all the way and how to enroll a Windows device with Autopilot using Azure Temporary Access Pass (TAP), and a FIDO2 security key. Working passwordless on Windows is easy, but when it comes to working passwordless on Mobile devices like […]
What is your excuse for passwords
What is your excuse for passwords and why is it, that we still heavily rely on passwords? Is it because passwords are easier to remember by end-users, or is it that someone thinks that end-users are not capable of handling anything else then a simple password. In other words, do we tend to think of […]